Why Should We Use Data Encryption While Online Communication?
April 15, 2024
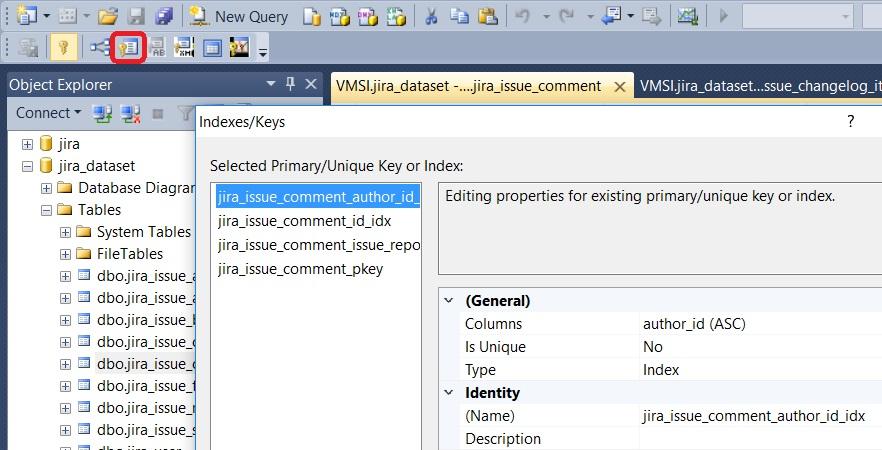
There are several good reasons for a company to invest in data encryption, but the main one is of course, protecting your online communication from leakage. One of the top recent examples is the failure that led to data exposure of more than 143 million customers of Equifax, one of the top three US lenders.
Even though the use of encryption cannot prevent theft of certain information, it can prevent the online communication data from being read and used in a way that harms the company. Let’s list the main reasons for investing in encryption technology:
Protect information in transit
Protecting information in transit is essential to prevent sensitive customer data, or strategic messages from being possessed by cybercriminals or malicious people. By encrypting these submissions only the recipient can make use of the key to verify the content. We recommend AITCA Messenger for fully encrypted business or personal online communication, available at here.
Protect cloud data
Cloud computing is here to stay, and cloud providers are increasingly investing in security to ensure that their customers’ data is not corrupted or accessed by unauthorized people.
However, an attack and data theft can always occur and even with all available tools, a leak has a chance of not being stopped.
Protect sensitive data
All companies have sensitive data, whether it is about their operations, business strategies, new products to be launched or even customer information under their control.
Attacks coordinated by competitors may look like a movie storyline, but they can’t be dismissed and believe me, they do.
Protect browsing
The use of mobile devices is very common today in companies. These tools enable employees to access company data through any internet link.
What happens is that navigation can often be done from a public network, such as libraries, shopping malls, and other environments that provide web access.